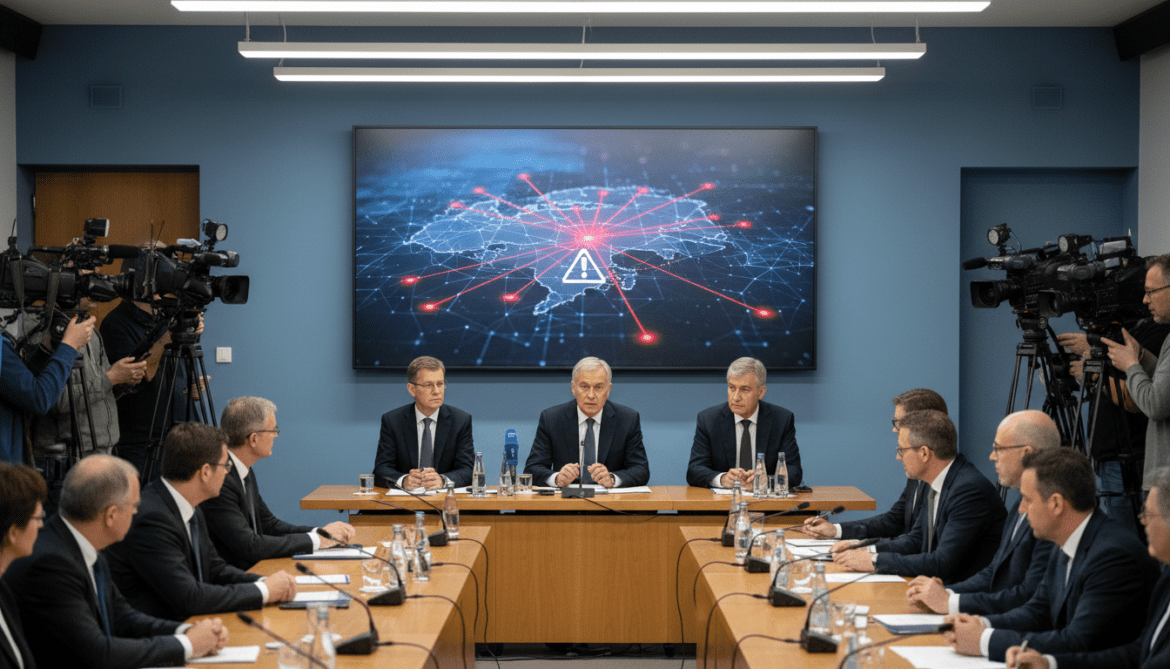
German Intelligence Warns Signal Accounts Compromised, Sensitive Data May Flow to Russia
German intelligence warns that compromised Signal accounts are leaking sensitive information to Russia; Bundestag groups and party offices were alerted.
A warning from the Federal Office for the Protection of the Constitution says Signal accounts compromised could be channeling large volumes of sensitive information to recipients in Russia, prompting immediate alerts to Bundestag parliamentary groups and party offices. The notice, addressed to political offices, highlights the risk to confidential communications and the potential exposure of internal documents and contact lists. Officials have been urged to review account security and to take immediate measures to mitigate further data loss.
Domestic intelligence issues alert to political offices
The Federal Office for the Protection of the Constitution issued the warning directly to Bundestag groups and party offices, signaling concern at the highest levels of domestic security. The agency characterized the threat as systemic and capable of producing a substantial exfiltration of material from affected accounts. Recipients of the notice were advised that the compromise was not limited to isolated individuals but could affect networks of linked devices and accounts.
Political offices were told to treat the alert as a priority, with instructions to audit recent communications and to identify accounts used for internal coordination. The notice emphasizes that even end-to-end encrypted services can be undermined when individual accounts or devices are compromised. Intelligence officials recommended immediate procedural checks and heightened vigilance for suspicious account activity.
Scope and nature of suspected exfiltration to Russia
The warning frames the issue as an active transfer of sensitive information to Russia, though details on the actors behind the transfers remain sparse in the notice. The agency cautioned that the content at risk includes internal party correspondence, strategy documents, and contact databases that could be used for political or intelligence operations. The characterization of the flow as “massive” in the advisory suggests the agency believes multiple accounts or coordinated intrusions are involved.
While the advisory names Russia as the destination for the data, it does not publicly assign responsibility to a named group or state service. Officials are continuing to assess whether the transfers represent opportunistic harvesting of credentials or a coordinated campaign targeting political actors. The significance of the data reportedly at risk has raised immediate concerns about national political security and the potential compromise of confidential sources.
How Signal accounts may be compromised
The advisory outlines a range of technical paths by which Signal accounts can be taken over or exposed when a device or its credentials are compromised. Common attack vectors cited by security experts include SIM swapping, interception of registration processes, malware on mobile devices, and unauthorized access to linked desktop sessions. Any successful takeover of the device or registration credentials can allow an adversary to read messages, obtain contact lists, or impersonate users.
Security authorities stress that the compromise of a single account can cascade if linked devices are not regularly audited or if protections such as registration locks are not enabled. The advisory advises a thorough review of linked devices, activation of all available account protections, and the immediate revocation of access for lost or unfamiliar devices. It also underscores the importance of keeping operating systems and messaging clients updated to close known vulnerabilities.
Instructions delivered to Bundestag and party offices
According to the advisory, recipients were instructed to cease sensitive communications on compromised channels until security could be verified and to move urgent conversations to vetted, alternative means. The alert recommended administrative reviews of devices used for party business, immediate password and PIN changes where relevant, and the activation of security features intended to prevent account re-registration. Offices were further urged to compile lists of potentially affected accounts and forward findings to relevant security bodies.
The notice also recommended limiting the use of personal devices for organizational communications and increasing reliance on centrally managed, secure endpoints where feasible. It called on party IT teams to coordinate with federal security authorities to conduct forensic checks and to implement mitigations tailored to each office’s threat profile. The guidance acknowledged the operational difficulty of immediately securing all accounts while stressing urgency.
Security services and political response
Federal security services have signalled they are tracking the matter and are prepared to offer support to affected institutions, though operational details and ongoing investigative steps were not disclosed in the advisory. Political offices have begun internal assessments, and some have temporarily suspended the use of specific communication channels for sensitive topics. Lawmakers and party officials are weighing both technical and procedural responses to limit further exposure.
The episode is likely to intensify scrutiny of how political actors use encrypted messaging in professional contexts, and whether additional safeguards or centralized platforms should be mandated for certain categories of communication. Security experts say the incident highlights the need for robust endpoint security and stronger account management practices alongside encryption.
Parliamentary and party IT teams face a short-term operational burden to implement the advisory’s recommendations while maintaining day-to-day functions. The domestic intelligence service has indicated it will continue monitoring developments and share further guidance as investigations progress.
The immediate priority for affected offices is to identify compromised accounts, isolate breached devices, and follow the security protocols recommended by the Federal Office for the Protection of the Constitution to prevent further leakage of sensitive material.